Our website contains links to partner sites. If you click from our site to the partner's site and purchase their services there, we will receive a commission for mediation (Find out more information). This form of cooperation does not affect the objectivity of our reviews. With each purchase made through links from our site, you support our editorial office so that we can create quality and useful content in the future. Thank you.
Understanding Your Digital Footprint: Importance and Tips for Better Online Privacy

Do you shop online? Do you use various marketplaces and groups for selling used items? Do you appear on social networks or discussion forums under your own name? Do you comment? Have you recently downloaded ebooks that you got for free in exchange for your email? How many online courses or webinars that you signed up for with your email address have you completed? How many times a day do you use a search engine to find various pieces of information? What apps do you use on your phone? Do you think that creating various nicknames or different email addresses is sufficient protection in today’s online world?
The list of activities on the internet could go on. Our daily lives are increasingly moving into virtual space. Every click, every interaction is recorded somewhere.
What Is a Digital Footprint?
A digital footprint is a collection of data and information that a user leaves on the internet or on electronic devices, which can be provided actively or passively.
An active digital footprint consists of information that you knowingly publish on the internet. This includes your personal details and profile pictures, as well as public posts on social networks, your comments and opinions in forums, and on various online platforms. It also includes lists of your favorite songs, books, products, and their reviews. Additionally, if you agree to share or use your GPS location, for example when searching for local services, these data also form part of your active digital footprint.

A passive digital footprint is made up of information that you provide in the online space unconsciously and that is not directly visible. For example, ordinary internet searches record details about your operating system, browser, and device, including the brand and model of your phone. These data help websites, including Google, to optimize the content displayed for your device (for example, a website is displayed differently on a computer and differently on a mobile phone, the content is adapted to the size of the screen), but at the same time, information about your habits and preferences when using the internet can be collected – what you searched for, at what time, from which IP address, and so on. They can be used for marketing purposes, for example.
It is important to maintain a steady and unified active and passive digital footprint. Consulting a professional such as the digital marketing agency DevriX will help you build and implement a successful marketing strategy that will help you generate more leads and loyal customers.
What Is a Digital Identity?
A digital identity is a complex reflection of your online activities and behavior, and may or may not reveal your real personality:
- For example, a personal profile on LinkedIn is a true reflection of your professional career.
- Other identities can be created with the intention of hiding your real identity. For the purpose of privacy protection or other reasons.
The number of digital identities that you can create on the internet is unlimited. Very often, it is not possible to unequivocally verify whether a digital identity corresponds to the real person who created it. That is why it is important to remain vigilant when communicating with unknown profiles on the internet.
Why Should You Pay Increased Attention to Your Digital Footprint?
It is said that the internet never forgets. A digital footprint is made up of various social, health, fitness, shopping, demographic, financial, employment data, as well as information about family and acquaintances. These data can be used in various ways:
- You may receive unsolicited phone calls, robocalls, spam emails.
- Websites often have embedded tracking codes from Facebook and Google, based on which they can monitor website visitation statistics and target advertising more precisely, remarket you.
- When applying for a job, there’s a high probability that the HR manager will visit your social networks or search for you on Google by your name and surname. If you have posted inappropriate photos in the past or presented inappropriate opinions somewhere in a discussion, it could disadvantage you during the selection process.
- Similarly, banks may follow this practice when approving loans and mortgages, or insurance companies when preparing insurance contracts, or your potential business partners if you are a company. The information they find about you through internet search engines can influence their final decision.
- The greatest damage can be caused by identity theft. Your data can be misused for withdrawing money from your accounts or purchasing goods on your account, establishing a new credit card, or obtaining various financial aids under your name (there are known cases where photos of oncological or pediatric patients were misused for setting up fake support collections).
- If someone gains access to your personal information, they can misuse it for doxxing. In doxxing, the perpetrator publishes your information (name, address, telephone number, email address, financial information, photograph, or any other personal data) online without your consent, often with the intent to intimidate or cause harm. This leads to harassment both online and offline and sometimes even to physical attacks.
- If someone gains access to sensitive or compromising information, they can use it to blackmail you.
- You can become a victim of harassment by a stalker. Stalking is repeated and unwanted following. This behavior includes a wide range of acts, such as constant calling, sending messages or emails, following or being present near the victim without their consent, obtaining information about the victim through the internet or other sources, as well as physical following or intrusion into the victim’s personal life.
- Sharenting is a compound of the words “share” and “parenting,” describing the situation when parents share information, photos, or videos of their children on social networks or other online platforms, for example, even to support the sale of various products. Sharenting raises important questions about the balance between the parental right to share and the child’s right to privacy. By sharing, you create a digital footprint that can affect the child in the future and increase the risk of misuse of this information by third parties.

Is It Possible to Delete Unwanted Information From Search Results?
Once you have published something, it will not be automatically deleted from the internet. However, under the GDPR regulation, you can request website administrators to delete your data, and also search engines to remove specific search results.
The General Data Protection Regulation (GDPR) sets various obligations for website owners regarding the protection of their visitors’ personal data, the most crucial from the perspective of your digital footprint are:
- Consent to process personal data: Websites must obtain clear and informed consent from users before processing personal data.
- Transparency: Websites must provide clear and understandable information on how users’ personal data are processed, including the purpose of processing and the recipients of the data.
- The right to erasure (“the right to be forgotten”): Websites must allow users to request the deletion of their personal data under certain circumstances.
For example, to delete search results in Google, you can use this form.
To delete your data from a specific website, look for instructions on how to request deletion in the Terms and Conditions or Privacy Policy, which should be published on the website. It can be bureaucratic and time-consuming to achieve deletion.
Can You Influence the Digital Footprint You Leave Behind?
Of course! By being cautious online, you can to a certain extent protect your data:
- Secure your accounts with strong passwords. Password management apps can help generate them.
- If possible, use two-factor authentication when logging into various accounts.
- Do not use Facebook or Gmail to log into other sites or services. In the event of a data breach at Facebook or Gmail, hackers could gain access to all the websites where you are logged in through them.
- Explore and adjust the privacy settings on all your social networks, keeping control over who can see your statuses, photos, and videos.
- Think carefully about what personal information you post on social networks.
- Do not share sensitive private information in emails, chats, public discussion forums.
- Avoid loyalty programs of stores. The data you provide upon registration will be used for marketing purposes, and additionally, the store can track your shopping habits and personalize ads for you.
- Cancel accounts in all services that you do not use.
- Do not allow location tracking in apps where it is not necessary.
- Use a VPN when connecting to public WiFi. We will advise you on choosing one in the article Best VPN: A Comparison of the 12 Fastest.
- Protect all internet-connected devices with antivirus programs.
Do You Know How to Check If Your Login Credentials for Various Services Have Been Hacked?
Unfortunately, data breaches sometimes occur. A so-called “breach” is a security incident in which data is unintentionally exposed in a vulnerable system, usually due to insufficient access controls or security vulnerabilities in the software. Hackers then sell the stolen data to third parties for profit. You can find a list of the biggest data breaches, for example, on the website “Have I been pwned?“.

On the mentioned website, you can also check if your email address is part of a data breach. Simply enter your email into the search box, click the “pwned?” button, and wait for the result.
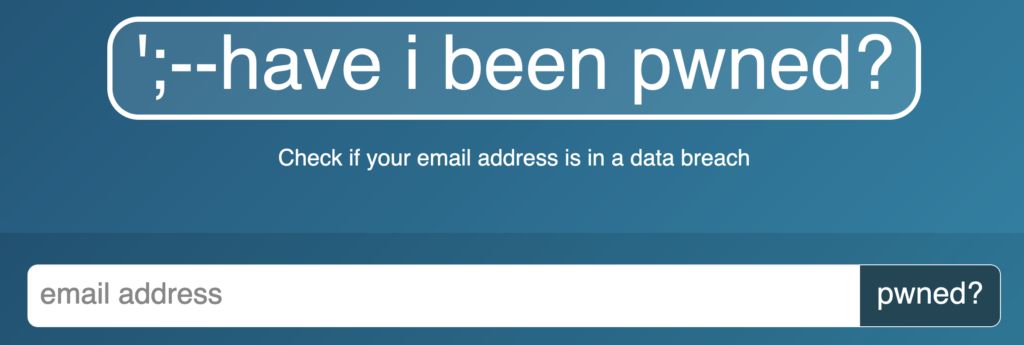
If your address was hacked, a list of data breaches in which it was available will be displayed. In such a case, we definitely recommend changing your password and, if possible, setting up two-factor authentication when logging in.
Incogni – A Service That Helps with the Removal of Your Data from Brokerage Databases

- Incogni is intended for residents of the USA, United Kingdom, EU, Switzerland, and Canada.
- Incogni collaborates with agencies and organizations for consumer rights protection.
- The Incogni service is designed in accordance with data protection laws – GDPR (General Data Protection Regulation), UK GDPR, and CCPA (California Consumer Privacy Act).
- Incogni has access to lists of data brokers.
- Incogni will verify if your data is present in any of the databases. Subsequently, it will request brokerage firms to delete your data from their databases.
- Approximately a month after the request is sent, Incogni will verify if the deletion has indeed occurred.
- During your subscription to Incogni, regular checks are performed to ensure brokers have not re-added your information to their databases.
- All these steps can be monitored in the Incogni application interface.
- Incogni is very advantageous for individuals because, in addition to protecting personal data, it saves time and provides legal support. If you were unaware of the existence of data brokerage firms before, you probably wouldn’t know where to find them. To provide sufficient legal arguments in requests for access to or deletion of your data from these firms’ databases, you would need to study legislation concerning personal data protection. Otherwise, these companies may ignore your requests.
- Incogni ensures that the request for removal from brokerage databases has a real impact.
Summary and Conclusion
In conclusion, understanding your digital footprint is not just about recognizing the data you leave behind online; it’s about taking proactive steps to control and protect that information. In today’s digital age, where privacy concerns are at an all-time high, it’s imperative to be aware of how your data is collected, used, and shared. By actively managing your digital footprint, you can safeguard your privacy, prevent identity theft, and maintain a positive online reputation. Remember, every click, share, and online interaction contributes to your digital legacy. Make it a priority to manage your digital footprint wisely, ensuring it reflects the image you wish to project to the world.
Read more of our articles on internet security. For example, how to stop unwanted phone calls if your data has been obtained by various marketing firms, or how to limit the delivery of spam to your mailbox.








